Lead Image © Yuri Arcurs, fotolia.com
Implementing custom security frameworks with Bro
Don't Hack Me Bro
Bro [1] is high-quality security monitoring tool designed to discover and analyze traffic trends on your network. Bro provides in-depth analysis of network traffic without limiting itself to traditional signature-based approaches. I first heard about the Bro network security monitoring framework when a consultant friend of mine talked about melding the world of big data and security together. My friend believed that traditional signature-based intrusion detection and monitoring simply wasn't enough to ensure a secure network.
The problem with networks is that, because of the increased number of devices, services, and tools used today, it's easy for attackers to enter networks in many different ways. Ransomware, botnets, malware, and remote control tools are readily available. Social engineering is especially prevalent now. Traditional intrusion detection and perimeter security tools just aren't up to the task.
Traditional monitoring tools are also having a hard time catching all of the anomalies. Bro, however, takes a different approach. The Bro framework is designed to monitor traffic on any layer. The default focus is on application layer traffic, but you can train Bro on any layer of the OSI stack. Bro is not really signature-based in its approach; it reviews traffic and looks for anomalous patterns. However, Bro also looks for similarities. It is ideal for setting baselines. Like many projects, Bro offers extensive commercial support.
Understanding Bro
The Bro application has three elements or layers:
- Monitoring engine: Software that listens to a network segment and reviews network traffic. This monitoring is similar to what Snort, Ntop, and other tools do. The engine also includes the event handler, which is designed to identify traffic and then act according to its configuration files.
- Policies: Files that determine how Bro will search the network. In addition to the monitoring engine, these policies are central to Bro's more novel approach to monitoring trends rather than focusing on known signatures.
- Logging engine: A component that organizes the information Bro captures.
With so many security projects in the open source/Linux space (see the box titled "Event Monitoring Tools") it is difficult to get excited about the latest and greatest software project. But Bro is a bit different. It's designed to fit a specific set of needs. Bro also happens to have been created at an appropriate time: It lets the user monitor events and then sift through them to find actionable information, not just data.
Event Monitoring Tools
Several powerful event monitoring tools are available today, including Snort [2] and AlienVault (OSSIM) [3]. Each has its strengths. Snort remains the premier signature-based IDS tool. OSSIM adopts a similar approach to Bro.
I wouldn't include Ntop [4] or Nagios [5] in this list. Both Ntop and Nagios are terrific software, they do monitoring, and they are actively supported. Yet Ntop is not designed to identify long-term security issues and trends. Nagios monitors network systems and servers; although it has a useful security component, it does not gather long-term information.
In today's security environment, most of my clients are asking for three things:
- Long-term attack analysis: It's not enough these days for IT professionals to set up real-time alerts of short-term scans. We all know that hackers are spending weeks and months surveilling and enumerating systems. Therefore, it's vital that today's security workers spend considerable time creating solutions that catch long-term attacks.
- An understanding of the unexpected places where the attackers are hitting them: Remember that old Monty Python skit where the folks storm in and yell, "No one expects the Spanish Inquisition?" CIOs and CISOs everywhere keep experiencing the hacker version of that joke; only, the results aren't so funny.
- Visualization: Business and IT professionals want easy-to-read representations of complex data.
Bro is really good at long-term attack analysis and understanding unexpected attacks; with a little help from its friends, it can also start you on the path to better visualization.
Installing Bro
It's best to install Bro from source. Although RPM and DEB binary packages are available, I have found they often don't work at all, or else they are missing some of the necessary software. The Kali Live Linux distro, a popular tool for penetration testing, comes with Bro installed by default, but I've found the Kali version doesn't work very well, either. You could try your luck, and your mileage may vary when it comes to the ready-made installation binaries that exist out there, but I know for a fact the source code installs on my Ubuntu 16.04 and Linux Mint systems.
The latest, stable version of Bro is 2.4.1. This latest version is the best documented version, and it works quite well. For those of you who have more intrepid natures, the 2.5 beta is available at the Bro website. I'll be sticking with 2.4.1 for this article.
Note: If you want to use Bro on a switched network, you will need to position Bro on a switch that allows your Linux system to monitor the entire network.
Start by installing the required dependencies. The dependencies, which are listed at the Bro website [6], include libpcap , OpenSSL, the BIND8 library, libz , Bash, and Python. Installing from source requires additional dependencies, including Swig, Bison, and Flex. I found that each of these dependencies was quite easy to install.
Once your system is ready, issue the following commands to install and compile Bro:
$ sudo apt-get install zlib $ sudo apt-get install zlib-headers $ sudo apt-get install cmake make gcc g++ bison libpcap-dev libssl-dev python-dev swig zlib1g-dev $ cd Bro-2.4.1/ $ ./configure -prefix=/nsm/Bro $ make $ sudo make install $ export PATH=/nsm/Bro/bin/:$PATH
If the PATH export doesn't work, you can also edit the /etc/environment file so that all new terminal instances can readily find where Bro is located.
Configuring Bro
Bro supports a pair of different approaches for interacting with the system:
- The
/etc/init.d/brocommand starts scripts that you can use to directly stop, start, and restart the application. - The
broctl(BroControl) command starts an interactive shell. You will live in this shell and use it to configure and manage the entire framework. With this command, you can activate interfaces, view statistics, and change the way Bro operates. Don't worry – it's a pretty intuitive environment.
Bro uses nodes
to control its framework. A node basically ties Bro's detection engine and rules to a particular interface and to a role. You configure a node in the /nsm/bro/etc/node.cfg file.
Another way to view a node is that it denotes a particular sniffing interface; you can configure multiple interfaces. It is possible to configure the following node types:
- Standalone: the system runs as a single node. If you are configuring a Standalone node, then make sure all other node types are commented out.
- Manager: the most powerful configuration after Standalone – used by those who not only want to view packets but also make changes to how Bro operates.
- Worker: For nodes that only view statistics.
Look for the Bro configuration and logfiles in the /nsm/Bro/etc/ directory – not the /etc/ directory. The files include:
node.cfg: where you create nodes.networks.cfg: where you specify the network to monitor.broctl.cfg: allows you to configure mailing options./nsm/bro/share/bro/policy/protocols: scripts configuration files./nsm/logs/: logfiles.
Start by configuring Bro so that it knows how to behave and knows the network. The node.cfg file determines how Bro will act. The networks.cfg file simply should include your current network, as well as any networks you want Bro to audit.
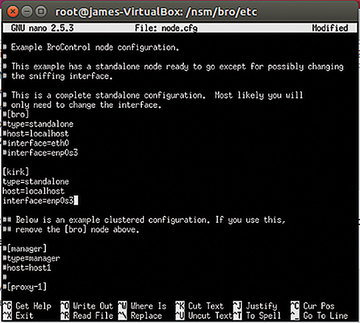
When editing node.cfg, it is possible to configure different nodes for the same interface. For the purposes of this article, I'll run Bro as a Standalone node. The first step is to configure the /nsm/bro/etc/node.cfg file (see Figure 1).
The default value is bro, but I decided to use kirk instead. Notice that the kirk node lists my own system, sets it up as a standalone system, and then specifies the interface. In this example, I'm using a virtualized Ubuntu system on a new-ish Ubuntu host, so the interface name is enp0s3
, rather than something standard such as eth0
or wlan0
.
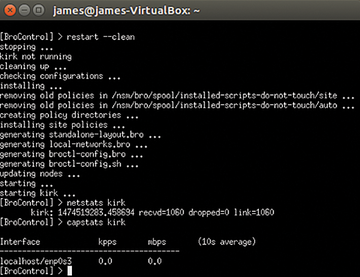
Once you have configured and saved your changes, you can then run broctrl as root to enter the interactive session. Once you enter the command
$ sudo -i broctl
you'll be placed into the interactive session, as shown in Figure 2.
From this session window, you can restart Bro to re-read any changes you've made in your configuration. You can also issue commands such as:
status: Used without arguments, thestatuscommand shows the status of all nodes. You can also specify a node (e.g.,kirk) to view only that particular node.deploy: Re-reads all system configuration files without restarting the Bro daemon process. You use this command without arguments.netstats: Provides statistics concerning all activated interfaces.scripts: Reports the scripts that Bro is using.top: Shows how much memory Bro is using.
See the Bro documentation for more on Bro commands [7].
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.