Lead Image © hketch, photocase.com
Microsegmentation with VMware NSX and vRealize Automation
Micro Net
Companies can easily and efficiently validate and control network traffic within the data center through microsegmentation. Microsegmentation is a collection of techniques designed to isolate network traffic through switching and software-defined networking. VMware's NSX for vSphere adds security to software-defined networking and microsegmentation, allows admins to filter network traffic at the level of the virtual machines (VMs) and network cards without installing an agent on the VM.
In traditional environments without NSX, traffic needs to be redirected for security checking using centralized security components that often exist as physical appliances. In NSX, traffic can be analyzed on the hypervisor itself.
NSX also supports automatic creation of logical, software-segregated, VXLAN-based networks, as well as network components such as firewalls, routers, gateways, or VPN endpoints. Automated solutions today reduce the deployment time for such applications from several days to just a few minutes – and with fewer errors, as the need for manual configuration is removed.
Extensive Set-Up Time
To provision both microsegmentation and network automation in the VMware environment, you'll need the vSphere Enterprise-Plus Edition (which supports distributed switches), vRealize Automation Advanced, and Orchestrator products in addition to NSX.
You'll need to start with some preparatory work on the vSphere and NSX side, including:
- Configuring a distributed switch in vSphere.
- Installing NSX, which includes preparing of the physical network, configuring VXLAN, defining segment IDs, and defining one or more transport zones.
Once you have completed these preliminary tasks, you can begin the actual work, which consists of:
- Preparing NSX for vRealize automation
- Creating an NSX endpoint in Orchestrator
- Configuring NSX vRealize automation
- Creating network profiles
- Applying the microsegmentation features to blueprints (a kind of building plan detailing the deployment process)
Preparing NSX for vRealize Automation
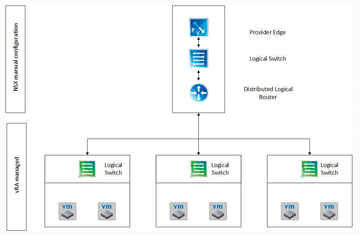
To set up NSX vRealize automation, you first need to create a provider edge gateway that connects the automated NSX world to the external network. In addition, you need to create a Distributed Logical Router (DLR) associated with the provider edge via an uplink. Ideally, this connection is made on the basis of a logical switch on the VXLAN that allows communication between the DLR and the provider edge gateway. The required configuration is shown in Figure 1. Setting up these components so that vRealize Automation can handle network automation and create logical switches at run time is a prerequisite. You can create all three required components of the NSX in the VMware vSphere web client.
To set up the logical switch, go to the Networking & Security menu in the GUI and select Logical switches . In the NSX Manager's NSX Manager Drop-Down List , select where the configuration should take place. Then press the [+] button to create a logical switch. You need to assign an appropriate name, optionally a description, and the replication mode (usually Hybrid or Unicast ). Finally, check the Enable IP Discovery box and press OK to finish the wizard.
Creating the provider edge is minimally less complex. First select the menu item NSX Edges in the navigation pane and then press the [+] button to launch the Create wizard. At this point, the configuration starts: In the first dialog, check the Edge Services Gateway box to choose to create an "edge" (a VM with routing functionality and possibly other functions), and enter a name, a description, and a tenant. If high availability of the edge is required, check the Enable High Availability box. Before you continue to the next page of the dialog, you need to enable the Deploy NSX Edge option. In the settings dialog box, specify a username, a password, and the SSH settings. Check the Enable Auto Rule Generation box and click Next .
The next step is to configure deployment. Define the CPU and RAM for the edge VM, and select the hypervisor on which the edge will be created. The network configuration of the edge deserves special attention in the further course of the configuration wizard. As mentioned, it is necessary to create two network cards: For communication with the outside world, you need an uplink network card, which is typically associated with a VLAN port group on a vSphere distributed switch. Configure the second interface as an Internal type, and connect it with the previously created VXLAN-based logical switch. You also need to define matching IP addresses and the Subnet Prefix Length for the two network cards. Choose 1500 as the MTU size. Once the configuration is complete, click Next .
The final steps are simple: First, define the default gateway and the MTU size on the Default Gateway Settings page, and choose to use the previously created uplink network interface card for external communication. On the Firewall and HA page, check the firewall security rules; then start the edge deployment process on the last page of the dialog.
The process of creating the DLR is similar to creating the provider edge, but in the first step of the wizard, you need to check the Logical (Distributed) Router box. In addition, you need to configure an uplink network card (which must be connected to the logical switch) and, if appropriate, the routing between the DLRs.
Creating an NSX Endpoint in Orchestrator
At run time, vRealize Automation does not create networks through direct communication with the NSX Manager but uses the vRealize Orchestrator orchestration engine as an intermediary. For this reason, you need to configure the Orchestrator to cooperate with NSX and create an NSX endpoint. Select the Workflow directory and run the Create NSX Endpoint workflow (library/NSX/configuration ). In addition to a name for the endpoint, you need to enter the appropriate access data and the URL of the NSX Manager.
After workflow execution has completed, check whether the setup has worked out in the Orchestrator inventory: If you can expand the NSX menu item, and if the corresponding NSX components appear, the configuration was successful.
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.