« Previous 1 2 3
Disaster recovery for Windows servers
Window Repairs
Cleaning Up Active Directory
When a domain controller is removed from Active Directory, you need to make some preparations so that users are not affected by its loss. Make sure the domain controller is not used as the preferred or alternative DNS server by any other computers in the domain (not even as a DNS forwarding server).
If possible, remove the DNS service from this domain controller before downgrading. In the DNS Manager on another DNS server, check in Properties that the server removed is no longer listed in the Name Servers tab. Do not remove the host entry for the server, as it is still needed for the downgrade.
Make sure that the domain controller is not explicitly registered as a domain controller at any point (e.g., on a Linux server or an Exchange server). Then, remove all Active Directory-based services, such as VPN, certificate authority, or other programs that will not work after the downgrade. Before the downgrade, first migrate all FSMO roles to other servers.
If there is a global catalog on this server, configure another server as the global catalog server and – in the Active Directory Sites and Services snap-in tool – under Sites | <Sitename> | Servers | <Servername> , right-click NTDS Settings, choose Properties , and uncheck Global Catalog in the General tab to remove the services for the old domain controller.
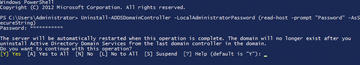
To downgrade a domain controller, your best bet is to use the PowerShell Uninstall ADDSDomainController Cmdlet (Figure 6). You still need to set the local administrator password via the command, which must be defined as a secure string in PowerShell. The syntax for doing this is:
Uninstall-ADDSDomainController -LocalAdministratorPassword (Read-\ Host-Prompt password -AsSecureString)
The Get-Help Uninstall-ADDSDomainController command gives you more information.
If you do not want to reinstall a domain controller that has lost its connection to the Active Directory, you can remove Active Directory, despite the lack of connection. In this case, use the -force option. The Active Directory metadata contains all the entries and server names that belong to Active Directory. If a domain controller is down or forcibly removed from Active Directory, the metadata needs to be modified retroactively.
To do this, you need to start the ntdsutil tool at the command line (Figure 7) and type metadata cleanup, followed by connections. Use connect to server <domain controller> to connect to the domain controller and enter quit to return to the metadata cleanup
menu.
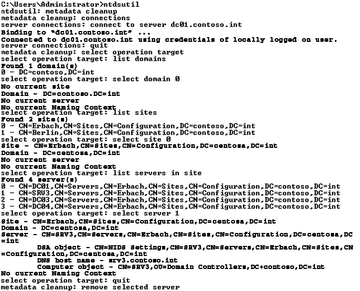 Figure 7: If a domain controller is not working, remove it from the domain and reinstall it. This approach is usually faster than a restore.
Figure 7: If a domain controller is not working, remove it from the domain and reinstall it. This approach is usually faster than a restore.
Enter select operation target and list domains for a list of all domains in the forest. Enter select domain <number of domain> to select the number of the domain from which you want to remove a domain controller. Entering list sites gives you all the locations in the forest; you can select one of them with select site <number of site>. The list servers in site command shows you all the domain controllers that are associated with this location, and select server <number of server> removes a server from the domain.
Again, enter quit to return to the metadata cleanup
menu. The remove selected server command first prompts you and then removes the server after confirmation.
After cleaning up the metadata in Active Directory, you still need to clean up the DNS entries. Start by removing all the SRV records that still point to the old server from the DNS zone of the domain; then, you can then delete the server's computer account. Delete the account under Domain Controllers in the Active Directory Users and Computers snap-in.
In the next step, you need to delete the domain controller from the site to which it was assigned. To do this, again use the Active Directory Sites and Services snap-in. Navigate to the location of the domain controller, select Delete in the pop-up menu, or press the Del key. Next, check the NTDS Settings of each domain controller in Active Directory to make sure that the domain controller is not registered as a replication partner and remove the connection if it is.
Fixing the AD Database
In some circumstances, the Active Directory database may stop working. Before you install a domain controller, you can try to repair the AD database. To do so, start the server in Directory Services Restore Mode
and call ntdsutil. Enter activate instance ntds, then files; this starts file maintenance
. Next, enter integrity; enter quit to leave file maintenance
.
Database analysis is launched by the semantic database analysis command. For a detailed report, choose verbose on
. If you enter go fixup the tool starts the diagnostics and repairs the database on request. Next, quit ntdsutil and restart the domain controller.
Exchange Backup
You can back up Exchange 2013 with the internal Backup Wizard in Windows Server 2008 R2/2012; the program also backs up the Exchange databases and supports online backups for Exchange databases. During the backup, the program performs a consistency check of Exchange files. Only when you restore can you select the Exchange databases.
Start a restore in the backup program via the Action menu. The Backup Wizard automatically de-provisions the database you are restoring and then provisions it again after the backup. The wizard guides you through selecting one of the local servers and defining the date and time of the backup you want to restore.
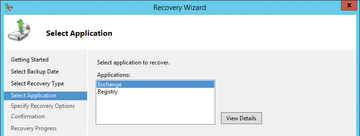
To begin, click Select Application in Select Recovery Type (Figure 8). The Exchange option must be listed under Applications . Then, you must ensure that an Exchange-compatible backup is available. View Details displays the backed up Exchange databases.
If the backup is the current version, a checkbox appears suggesting Do not perform a roll-forward recovery of the application databases . For a roll-forward recovery, you need the transaction logs that were created after the backup. Exchange then writes them to the database to complete the recovery. If you enable the Recover to Original Location option, the backup program restores all backed up databases in their original locations.
After restoring, you can integrate the data files into a recovery database and then manually move them back to their original location, or you can restore individual data from the backup.
Infos
- BlueScreenView: http://www.nirsoft.net/utils/blue_screen_view.html
- Seatools: http://www.seagate.com/support/downloads/seatools/
- Data Lifeguard Diagnostic: http://support.wdc.com/product/download.asp?groupid=810&sid=3&lang=en
- Drive Fitness Tools: http://www.hgst.com/support/index-files/simpletech-legacy-downloads#DFT
« Previous 1 2 3
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.