Intruder Detection with tcpdump
Tcpdump is a general-purpose packet sniffer and incident response tool that should be in your tool shed.
Tcpdump is a widely used and powerful tool that captures, parses, and analyzes network traffic. Created by the Network Research Group at Lawrence Berkeley National Laboratory, Berkeley, California, tcpdump (http://www.tcpdump.org) is deployed with libpcap (a C/C++ library for network traffic capture) and maintained by the libpcap developers (http://sourceforge.net/projects/tcpdump/). With tcpdump, you can analyze large binary files that are too large to view casually with a tool like Wireshark by whittling your file down to only the information pertinent to your investigation. Most distributions have tcpdump installed by default, but if not, use your distro’s package manager. The SourceForge link above has project information as well as the code.
Tcpdump runs locally on your machine and can read or write network traffic information to a file. A basic capture uses the syntax
tcpdump -n -i-s
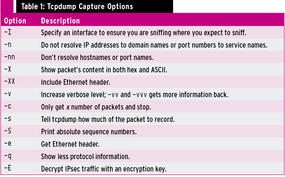
where -n means tcpdump should not resolve IP addresses to domain names or port numbers to service names, -i <interface> is the interface to use, and -s specifies how much of the packet to record – I use 1515, which is sufficient for most cases, but if you don’t specify a size, it will only capture the first 68 bytes of each packet. Except in older versions of tcpdump, a snaplen value of 0 uses a length necessary to capture whole packets. Figure 1 dissects the output of a sample dump, and Table 1 shows more examples of tcpdump options and when to use them.
File Read and Write
Tcpdump allows you to write to a file with the -w option and read from a file with the -r option:
$ sudo tcpdump -i wlan0 -w dumpfile001 $ sudo tcpdump -r dumpfile.pcap
If you want to see the files as they are captured and save them to a file, use the following options:
tcpdump -n -i eth1 -s 1515 -l | tee output.txt
This command tells tcpdump to line-buffer its output, and by piping to the tee utility, it sends output to the screen and output.txt simultaneously, but not in binary format. The best way to do that is run a second instance of tcpdump.
Timestamps
When tcpdump captures packets in libpcap format, it adds a timestamp entry to the record in each packet in the capture file. Monitoring software like tcpdump uses libpcap to capture packets traveling over a network, read saved capture files, and analyze them, and you can augment that data with the -tttt flag, which adds a date to the timestamp (Figure 2).
If you are not sure you understand the time differences reported and need to be absolutely sure of time, use the -tt option to show seconds and microseconds since the beginning of the Unix epoch (00:00:00 UTC on January 1, 1970) (Figure 3).
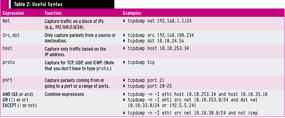
The useful expressions in Table 2 can help you cut the amount of traffic down to just what you need.
Searching for Packet Information
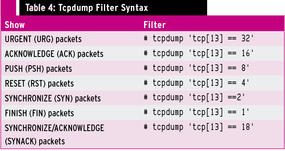
If you want to search for information in the packet you have to know where to look. Tcpdump starts counting bytes of header information at byte 0; the 13th byte contains the TCP flags shown in Figure 4.
Looking at byte 13, if SYN and ACK are set, then your binary value would be 00010010, which are the same as decimal 18. This command searches for packets with this type of data in byte 13:
# tcpdump -n -r dumpfile.lpc -c 10 'tcp[13] == 18' and host 172.16.183.2
Figure 5 is an example of what this command will return.
When capturing data with tcpdump, one way to ignore the ARP traffic is to put it in a filter:
# tcpdump -n -s 1515 -c 5 -i eth1 tcp or udp or icmp
This will catch only tcp, udp, or icmp.
Tables 3 and 4 show you what you need to know to find all TCP packets with the SYN ACK or other flags set.
Incident Response
When analyzing network traffic, a tool like tcpdump is critical. I'll share some examples of using tcpdump to view a couple of different dump files as a way to learn more about network problems or possible attack scenarios. The first is a binary dump file of a snort log. You have the following information: The IP address of the Linux system is 192.168.100.45; an attacker got in using a WU-FTPD vulnerability and deployed a backdoor. What can you find out about how the attack happened and what the attacker did?
First, take a look at the file:
# tcpdump -xX -r snort001.log
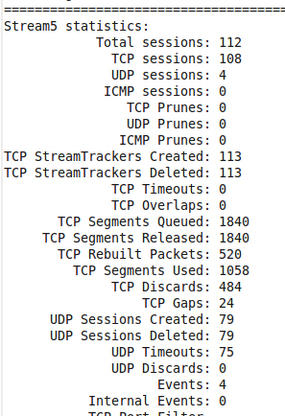
The log appears long at this point, so you might want to run the file in snort,
# snort -r snort001.log -A full -c /etc/snort/snort.conf
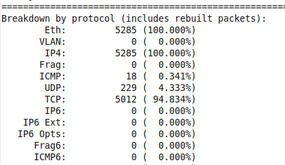
which gives you information like total packets processed, protocol breakdown, alerts, and so on (Figures 6 and 7).
Next, extract the full snort log file for analysis,
# tcpdump -nxX -s 1515 -r snort001.log > tcpdump-full.dat
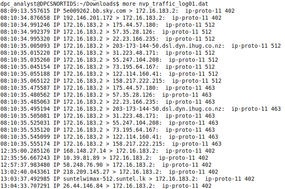
which gives you a readable file to parse. After looking through it, you find ip-proto-11, which is Network Voice Protocol (NVP) traffic. Now you can search through the file looking for ip-proto-11.
# tcpdump -r snort001.log -w NVP-traffic.log proto 11
This command reads the snort001.log file, looks for log proto 11, and writes the contents to the NVP-traffic.log file. Next, you need to be able to view the binary file.
# tcpdump -nxX -s 1515 -r NVP-traffic.log > nvp-traffic_log.dat
This file contains both hex and ASCII, which is nice, but you just want the IP address. Try this,
# tcpdump -r NVP-traffic.log > nvp-traffic_log01.dat
which gives you a list of IP addresses that were communicating by Network Voice Protocol (NVP) (Figure 8).
Next, I'll show you another snort dump file from a compromised Windows box that was communicating with an IRC server.
With which IRC servers did the server at 172.16.134.191 communicate? To look for TCP connections, try using tcpdump with a filtering expression to capture SYN/ACK packets coming in from outside servers:
# tcpdump -n -nn -r snort_log 'tcp and dst host 172.16.134.191 and tcp[13]==18'
This command produces a long list of connections going from 172.16.134.191 to outside connections (Figure 9).
Because IRC communicates on ports 6666-6669, add that information to the command to narrow down the search:
# tcpdump -n -nn -r snort_log 'tcp and dst host 172.134.16.234 and tcp[13]==18' and portrange 6666-6669
Now the list has been narrowed down to three IPs that were communicating with the server using IRC (Figure 10).
The Author
David J. Dodd holds a current Top Secret DoD Clearance and is available for consulting on various Information Assurance projects. A former US Marine with an Avionics background in Electronic Countermeasures Systems, David has given talks at the San Diego Regional Security Conference and SDISSA. He is a member of InfraGard and contributes to Securing Our eCity (http://securingourecity.org). He works for pbnetworks Inc. (http://pbnetworks.net), a service-disabled-veteran–owned business located in San Diego, CA. You can contact him by emailing dave@pbnetworks.net.