The light-footed Hiawatha web server
Frugal Delivery
Most admins intuitively think of Apache first when they hear "web server." The program is not only one of the longest serving of its kind, but it has built a reputation over the years of being a smart and stable product.
Admittedly, there are other options: in the eyes of many admins, Nginx has long since become the better option. If you can't handle the massive feature set of Nginx or Apache, you'll regularly end up with Lighttpd, which is limited to the bare essentials in many respects. Only rarely do admins settle on Hiawatha (Figure 1).
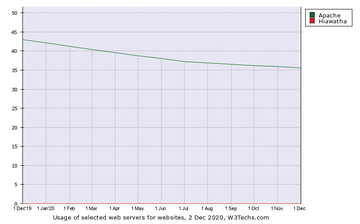 Figure 1: The W3Techs survey lists very few installations of Hiawatha, but that doesn't begin to do justice to the server's capabilities. © W3Techs
Figure 1: The W3Techs survey lists very few installations of Hiawatha, but that doesn't begin to do justice to the server's capabilities. © W3Techs
The bottom line is that Hiawatha [1] very much offers a valid alternative to Apache, Nginx, Lighttpd, and other web servers if you don't need exotic features. In this article, I introduce Hiawatha, detail its genesis, and describe how admins can get up and running quickly with the solution.
What Hiawatha Can Do
Anyone researching Hiawatha on the web will be confronted with a variety of possible explanations for the
...Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.



