« Previous 1 2 3 4 Next »
Portable home directory with state-of-the-art security
Home, Sweet Home
Your home directory (~) stores personal data and configuration files for the programs you use (e.g., the Google Chrome or Firefox profile and the GTK configuration for the look and feel you prefer for the installed desktop). Moreover, your home directory also contains Thunderbird mail, your music collections, and your photos. Like your own home, the personal folder on a Linux system is typically a place you want to keep safe.
If you use more than one Linux computer, you will not find your personal files on all of these devices, and fixing this issue is by no means trivial. The question of what users can do to share their home directory efficiently with a variety of systems is not new.
Systemd boss Lennart Poettering finally came up with a solution – Homed – that works on recent systems, relying on systemd in the background and making it possible for users to take an external disk with their home directories from machine A to machine B and on to machine C without getting into any trouble (Figure 1).
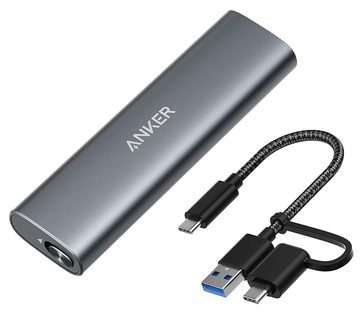 Figure 1: M.2 SSDs (for high-performance storage in power-constrained devices) are so small and light that even
Figure 1: M.2 SSDs (for high-performance storage in power-constrained devices) are so small and light that evenBuy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.




