
Photo by Önder Örtel on Unsplash
Acorn facilitates the deployment of apps in Kubernetes
Smart Assistant
Distributors such as Red Hat and SUSE have been working to turn their large enterprise distributions into container runtime environments to outsource much of the hassle of package maintenance to the vendors of programs. In this and many other places, the motto "Kubernetes first" applies. Infrastructure as Code and continuous integration/continuous deployment (CI/CD) pipelines with all kinds of automatisms, including implicit error correction, are attractive factors simply missing in conventional deployment models.
For some admins, however, getting used to the world of containers and fleet managers quickly becomes a nightmare. Kubernetes and the container lobby promise that they will make everything far simpler and easier to manage. However, if you are setting up Kubernetes (K8s) for the first time and need a configuration that is not provided in the default settings of the respective K8s distribution, you will find yourself at a complete loss (Figure 1).
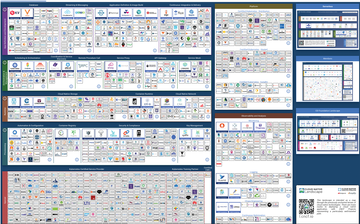 Figure 1: Kubernetes is powerful, but it is also massively complex. The sum of different technologies and functions that have formed around K8s in particular leaves newcomers perplexed. © CNCF
Figure 1: Kubernetes is powerful, but it is also massively complex. The sum of different technologies and functions that have formed around K8s in particular leaves newcomers perplexed. © CNCF
The
...
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Focus On Self-Hosting
• Self-Hosted PaaS with Coolify
• Build and Host Docker Images
• Self-Hosted Pritunl VPN Server with MFA
• Self-Hosted Chat Servers
• Self-Hosted Remote Support with RustDesk
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.





