« Previous 1 2 3 Next »
FreeRADIUS for WiFi hotspots
Large Radius
Do you know someone who keeps the WiFi password on a piece of paper under their keyboard? Or somewhere equally as insecure? Sloppy password practices are a nightmare for any admin; controlling access to the company network is impossible with a shared password, even if you have a manageable number of employees.
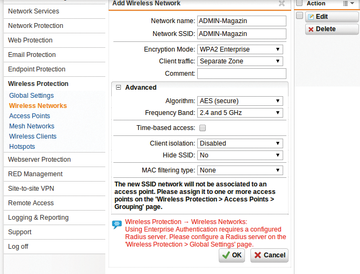
How do you implement security on a WiFi network without a shared password? One solution is IEEE 802.1X, a standard mechanism for network authentication. For enterprise WiFi hotspots, this login procedure usually goes by the name of WPA Enterprise (Figure 1).
In most cases, the user database is not managed by the hotspot itself. Instead, the hotspot queries a RADIUS server on the same network (Figure 2): The central user administration actually takes place on the RADIUS server. If you take on a new employee, you enter their account on the RADIUS server, WiFi access included.
...Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.