« Previous 1 2
Configuration management and automation
Launched
Automation software such as Ansible is popular with admins, but occasionally other colleagues need to step in to perform jobs on servers, and not everyone is a big fan of the command line. Rundeck [1] is the perfect software tool for these tasks because it lets admins configure tasks that others can then perform, such as build processes or even simple things like rebooting a server. Rundeck's highly granular access controls let you configure the appropriate rights for users and groups, as well as configure and map complex workflows with dependencies (Figure 1).
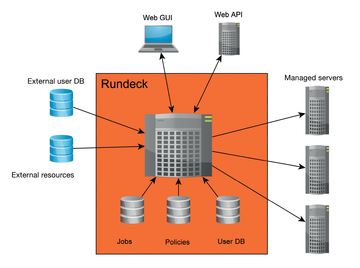 Figure 1: A Rundeck server can be controlled using the web GUI or the API. In addition to local resources, external resources can be integrated.
Figure 1: A Rundeck server can be controlled using the web GUI or the API. In addition to local resources, external resources can be integrated.
Thanks to a series of plugins, Rundeck can also be used in conjunction with popular tools like Puppet, SaltStack, and Ansible. Rundeck integration for Foreman lets you export managed hosts from Foreman for Rundeck. Even cloud environments are not unknown territory, because Rundeck has plugins for Amazon Web Services (AWS). If you need high availability, multinode clusters, or centralized logging, you can also take a look at Rundeck Pro. Additionally, the Rundeck developers at SimplifyOps also
...Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.






