« Previous 1 2 3
Attacks on HTTPS Connections
Tapped in
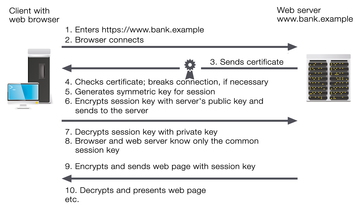
HTTPS couldn't be simpler from a user perspective: If you establish a secure connection (e.g., to a bank) in a web browser via an HTTPS link, your browser initially establishes an unencrypted connection to the specific server (Figure 1). The server identifies itself with a certificate containing its public key and the signature of a trusted third party, called a certificate authority (CA). The CA confirms by signature that the key belongs to the server specified in the certificate. Your browser then checks the certificate. To do so, it has a list of CAs that are trusted by the browser manufacturer. If the certificate wasn't issued by one of these CAs or the signature isn't correct or doesn't match the server, the browser displays a warning and terminates the connection, unless you need the potentially unsafe connection anyway.
If the check is successful (or if you agree to the connection despite the error), the browser generates a symmetric key that is only used for the current session, the session key. The key is encrypted with the web server's public key and sent to the web server. Once the web server has decrypted the session key with its private key, both web browsers and web servers have a common key for the symmetric encryption process that can then be used to encrypt all other
...Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.