« Previous 1 2
Improved defense through pen testing
Black Hat, White Hat
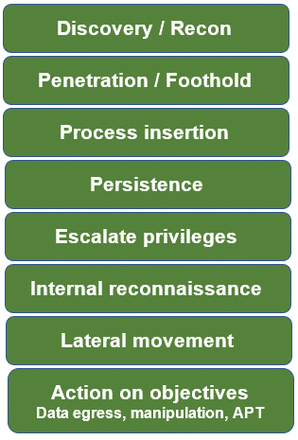
Cybersecurity professionals often call the steps taken by pen testers the "hacker lifecycle." In a previous article [1], I outlined the pen test discovery process. In this article, I focus on the typical steps that pen testers undertake to automate and orchestrate attacks (Figure 1). In a future article, I will show how each of these steps can be detected by a good security analyst with the right tools.
Although more than a single hacker lifecycle exists, Figure 1 shows many of the steps that most attackers will take when compromising a resource in the cloud – or even in a traditional network. I've seen quite a few useful pen testing/hacker lifecycle models, and although none are perfect, two of the more popular models are the Cyber Kill Chain© (copyright Lockheed Martin) [2] and the MITRE ATT&CKTM model [3].
Rather than say that all models have their strengths and weaknesses, I would argue that a good pen tester will customize and alter basic steps along the way according to the nature of the organization being tested. The main steps will be similar; however,
...Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.