« Previous 1 2 3 4 Next »
Foundries.io IoT development platform
Conundrum Solver
If you want to see die-hard system administrators go mad, all you need to do is bring up the topic of the Internet of Things (IoT). Virtually no other a topic will unite Linux admins in such a unanimous opinion. Stories offer examples of IoT applications that have gone wildly wrong. Many of these are urban legends and never actually happened, but they fit beautifully into the narrative of technology that doesn't really help anyone, opens security holes, and, in the eyes of many, simply shouldn't exist.
However, valid IT approaches do exist, and IoT devices perform well every day. The fact that the nation's discounters regularly offer WiFi-capable cameras with woeful security measures should not obscure the fact that in many places around the world, networked WiFi cameras with good security can protect people. In other words, IoT applications often are not as useless as some people would make them out to be (Figure 1).
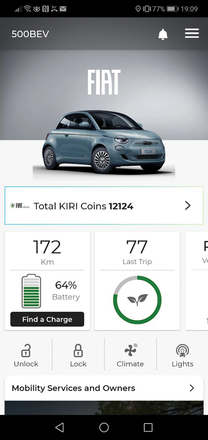 Figure 1: Today, even cars have an Internet connection and communicate over a smartphone, making them part of the Internet of Things.
Figure 1: Today, even cars have an Internet connection and communicate over a smartphone, making them part of the Internet of Things.
This is where Foundries.io steps into the breach by offering Foundries Factory as a complete solution for companies that want IoT functionality but do not want to deploy the entire infrastructure in-house.
...Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.




