Safe as Houses
As a desktop firewall, Windows Firewall has the task of protecting the local computer; thus, it differs in principle from network firewalls, which control data traffic between networks. The local firewall has certain functional requirements. The main task, of course, is keeping out undesirable data traffic from the outside. Although the old Windows Firewall handled this job well, Windows Firewall with Advanced Security adds many new features:
- Controlling outbound data traffic
- Complex rules for inbound and outbound traffic
- Profile-based rules
- Signed and encrypted communication
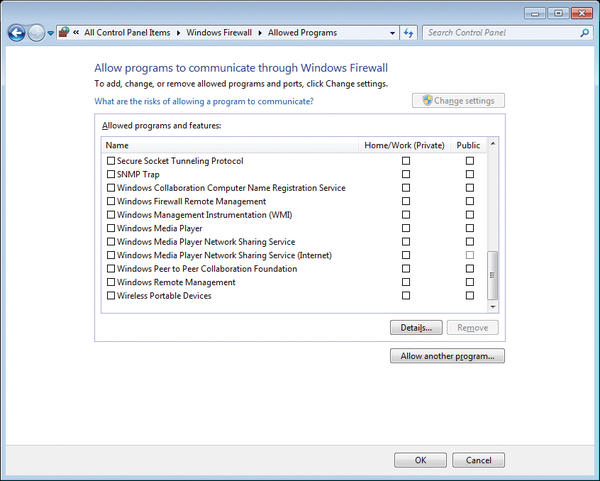
The user has a choice between the simple firewall view and the Windows Firewall with Advanced Security snap-in. The simple view is accessed via the Control Panel by pressing the Windows Firewall icon. Here, you are also introduced to the concept of network locations (explained later) because the configuration of Windows Firewall is defined individually for each kind of location (Figure 1).
 Figure 1: You can define the Windows Firewall configuration individually for each kind of location, such as Home or work (private) networks.
Figure 1: You can define the Windows Firewall configuration individually for each kind of location, such as Home or work (private) networks.
Simple View
To modify the default configuration of Windows Firewall in the simple view, you select Allow a program or feature through Windows Firewall then the Change settings button to enable the selection window. Now you can either select the desired programs and features from the list by checking the appropriate boxes or press the Allow another program button to select a program that is allowed to communicate through the Windows Firewall (Figure 2).
Because any program can send connection requests in the default setting, this point relates in particular to incoming connection requests, which are not generally allowed until you create a corresponding rule.
In the simple firewall view, you can also switch Windows Firewall on and off specifically for each network location. Disabling the firewall temporarily is particularly useful for testing – for example, if you want to rule out that possibility that communication is being blocked by the firewall.
Incidentally, an interesting trick allows you to determine whether a firewall is blocking communications between your local system and a computer on the same subnet. As a first step, you can try to contact the desired communication partner using Ping, which might or might not provoke a response. Then, look at the ARP cache with the arp -a command. The output of the arp command shows the IP address assignments and the corresponding MAC addresses. If the MAC address of the target system is shown correctly, in almost all cases, a firewall is to blame for the communication failure. If the MAC address is not shown, however, the target system is probably not active. This technique only works on local networks and not across router boundaries.
In the simple view, you can restore the default configuration of Windows Firewall. To do so, select the Restore defaults menu item. This option affects all network locations and resets all firewall settings to the factory defaults. Additionally, you can Change notification settings , which opens the same window that lets you enable or disable the Windows Firewall. The only notification setting you can modify is the one that enables notification when a new program is blocked. Make sure that you press the Back button to go back to the main view, because the feature does not open a separate window. If you click the corner Close icon here, the entire Firewall view is closed, including the Control Panel.
Advanced View
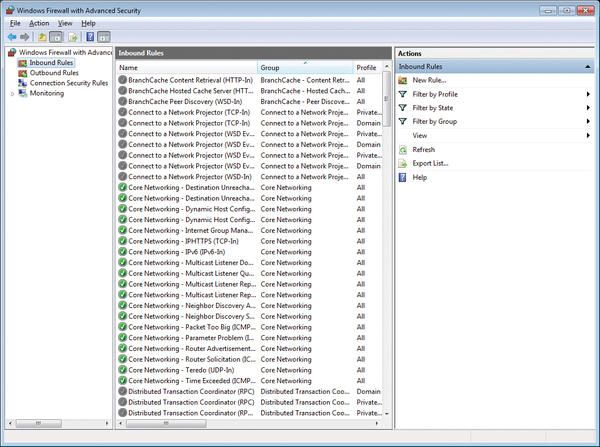
To access Windows Firewall with Advanced Security, either select the Advanced settings menu item in the standard view or type wf.msc in the combobox of the Start menu. This opens a management console (MMC) with the usual three-panel setup: the menu on the left, actions on the right, and content to reflect the context in the main window in the middle (Figure 3). The first overview shows the configuration (Profile) of the individual network locations.
Network Locations and Profiles
Irritatingly, locations are also known as network addresses (e.g., in Windows Help). A network location or network address in the sense of MMC is a set of security settings that are automatically enabled when the computer is connected to a network. Four network locations are distinguished:
- Home network: You should only activate this configuration in highly trusted environments. You can create a Homegroup here that allows largely unprotected access to personal folders on other computers in the same Homegroup. The Homegroup is a kind of mini-domain for home use.
- Work network: Designed for small business networks, this location is also suitable for trusted environments. Access to shares is possible and the network discovery mechanisms are active so that computers on the network can be found and can find other computers.
- Public network: If the computer is on an unprotected, public network, this location is useful to prevent access to the computer from the outside. Network discovery is disabled, and access attempts from the outside are ruled out.
- Domain network: This network configuration is automatically activated if the computer joins an Active Directory domain. It is managed by the administrator of the domain and cannot be selected.
You can select the desired network location in the Network and Sharing Center, and you can modify the network type in the View your active networks section. The network location settings include various mechanisms, whereas the firewall profile defines the Windows Firewall settings. All rules can be enabled or disabled separately for individual profiles; however, the settings for the home and work networks are grouped under the Private Profile.
The basic behavior of the Windows Firewall can be configured for each profile. To do this, pop up the context menu for the topmost entry in the menu on the left and select Properties . In the basic settings, you can, for example, configure how the firewall behaves when inbound or outbound connections are not explicitly covered by a rule. By default, all incoming connections are blocked and outbound connections are allowed (Figure 4).
Rules
The left pane of the main window shows the three areas in which you can change Firewall rules:
- Inbound Rules: These rules apply to all communication requests from the outside.
- Outbound Rules: These rules control communications originating from the local computer.
- Connection Security Rules: This section allows you to select communication settings for authenticating, encrypting, or both.
The right pane of the main window shows the existing rules created for the area chosen in the left pane (e.g., for Inbound Rules in Figure 3). Various preconfigured rules exist in Windows. The overview window contains a number of columns that show the settings for each individual rule. The Action of a rule consists of one of the following options: allow, block, and allow if secure.
The intended action is shown by the icon in the first column of the rule name. A distinction is made between active and inactive rules. The icon is grayed for inactive rules. In the basic settings, in particular, there are many rules for various uses, which you can enable as needed. To do this, double-click the rule and check Enabled .
Programs can insert their own rules during the install. For example, games regularly add various rules to the ruleset for inbound rules. On Windows servers, rules are added for the different server services when they are installed. Depending on the scenario and environment, it is possible that you, as the administrator, only very rarely actually need to add rules manually.
Creating a New Rule
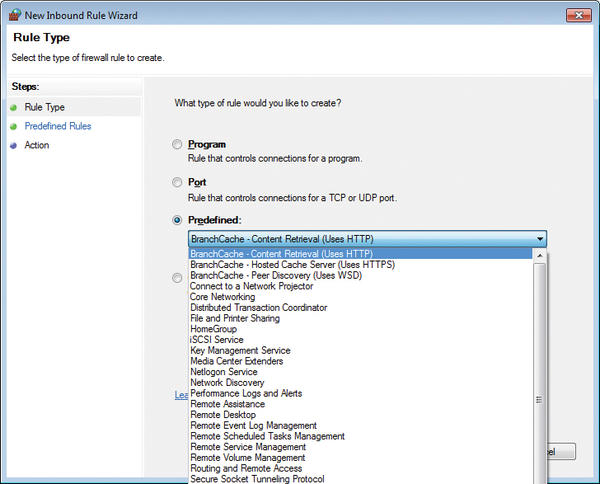
To add an inbound rule, select the New Rule item in the context menu for Inbound Rules . You can decide whether the rule allows or blocks a program or a port. An allowed program can bind to any port and be addressed by any means from the outside.
Alternatively, you can select a suitable rule from a list of predefined rules (Figure 5), which makes sense, for example, if you are enabling the branch cache feature.
You can only access these configuration options if you select Custom . First select whether the rule will apply to a specific program or be independent of a program. The next step is either to select a protocol type (e.g., TCP, UDP, or ICMP) or to keep the protocol type All . Depending on your selection, the input mask enables or disables the protocol-specific information. Of course, you cannot select ports for the ICMP protocol. Conversely, you cannot select ICMP settings for TCP or UDP.
The next dialog box allows you to select the source and target addresses, which are referred to as local and remote . Typically, only restrictions on remote addresses will be relevant. In the input field, you can enter both IPv4 and IPv6 addresses. They can be host or network addresses. Address ranges are also possible. Examples are shown below the entry field. Finally, you need to define the action, as discussed previously. Now the rule requires a profile mapping and a name, after which the rule appears at the top of the rule list, but only temporarily.
When you reopen the snap-in or sort a column, the rule is sorted accordingly. Incidentally, the second column shows a Group assignment for pre-defined Windows rules, so you view and manage related rules sorted by group (e.g., using NetShell (netsh ) to enable or disable them). Any rules you create are activated immediately.
To view the properties of existing rules, you can double-click a rule or select Properties from the rule’s context menu. If this is a predefined rule, you cannot change the properties. For all other rules, you can customize each parameter of a rule retroactively.
Outbound Rules
The Outbound Rules selection also contains various predefined rules. Many of these rules are disabled, and the allow action may be defined for individual rules that have already been activated. However, these rules are not really relevant unless the default rule for the active profile is set to block , which is not the case by default. In normal circumstances, the Windows Firewall will allow any outbound communication that is not explicitly blocked. As long as the default rule for outbound connections is set to allow , outbound rules only make sense if they either block a specific communication or require a secure connection.
Evaluation Order for Rules
Windows knows a number of rule types in addition to those discussed thus far. The order of internal processing is as follows:
- Windows service hardening
- Connection security rules
- Authenticated work-around rules
- Block rules
- Allow rules
- Default rules
The Windows Firewall follows an approach that is different from other firewalls that process rules as individually ordered. When creating rules, you must take this into account.
Connection Security Rules
The connection security rules complement the normal ruleset that allows or blocks connections. If you indicate that only secure connections are to be allowed for a rule, the communication must match one of the rules created in the Connection Security Rules section. Unlike inbound and outbound rules, these rules have no defaults.
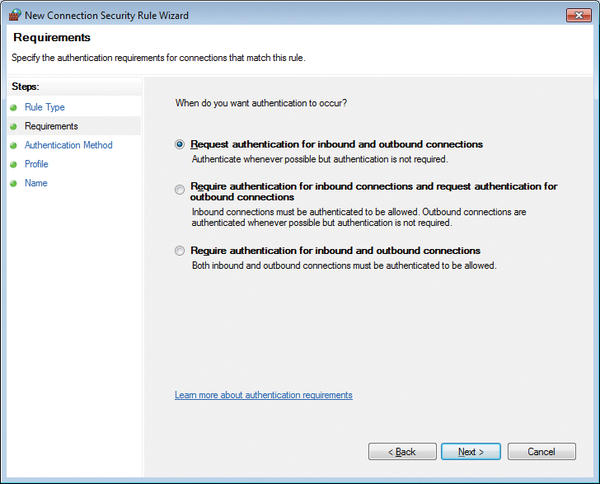
Connection security rules are created in the same way as inbound and outbound rules. After selecting New Rule in the context menu, you can choose between different rule types:
- Isolation: Restrict connections based on authentication criteria, such as domain membership or health status.
- Authentication exemption: Do not authenticate connections from specific computers.
- Server-to-server: Authenticate connection between the specified computers.
- Tunnel: Authenticate connections between gateway computers.
If you select Isolation , the computer is protected against non-authenticated computers. On the next dialog page, you can select the authentication requirements for a particular rule’s connections (Figure 6).
The next step lets you define the authentication method that the rule will require. In this case, you can select whether to use IPsec settings or Kerberos authentication, which requires membership in a domain. After you assign a name to the new rule, it is created and appears in the main window. Caution: The rule you just created is enabled immediately! If you create a restrictive rule and the remote systems are not configured appropriately, the computer will be isolated. If you want to allow connections only via a certain inbound or outbound rule, if the connection is secure, you can select the corresponding action in the rule properties. Press the Customize button for more settings, for example, to enforce encryption.
Managing Rules via NetShell and PowerShell
You can easily configure the Windows Firewall through the graphical interface. Selecting Computer Configuration | Windows Settings | Security Settings | Windows Firewall with Advanced Security launches the well-known dialog wizard in which you can create specific rules for inbound and outbound network traffic, as well as connection security rules. However, you can also query and configure the Windows Firewall at the command line with a scripting tool like NetShell. The command
netsh advfirewall firewall show rule name=all
lists all firewall rules. If you want to disable the firewall, you can do so with the following command for all profiles:
netsh advfirewall set allprofiles state off
To reenable, use the same command, but with state on . To create a rule that allows inbound pings:
netsh advfirewall firewall add rule name="Incoming ICMPv4" dir=in action=allow protocol=icmpv4
The rule is active and is also displayed in the ruleset below Inbound Rules .
PowerShell also supports configuration of Windows Firewall. However, PowerShell is not as straightforward as using NetShell commands. If you are using PowerShell, interaction with the Windows Firewall is handled via the HNetCFG.FWPolicy2 COM object, and the configuration requires advanced scripting skills.
Tips and Conclusions
Windows Firewall with Advanced Security provides some new features that weren't present in previous Windows Firewall versions, including support for more complex rules. The new firewall distinguishes individual network locations, which are stored as profiles. By default, outbound connections are always allowed for all profiles.
Windows Firewall with Advanced Security allows you to name the programs for which communication is allowed or blocked, and it also lets you harden communications using IPsec.
The Author
Eric Amberg is the managing director of ATRACON GmbH. He has worked for many years in the field of IT infrastructure as a trainer and consultant and has many years of project experience. His main focus is on networking topics. In his seminars, he lays great emphasis on practical training.
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Focus On Self-Hosting
• Self-Hosted PaaS with Coolify
• Build and Host Docker Images
• Self-Hosted Pritunl VPN Server with MFA
• Self-Hosted Chat Servers
• Self-Hosted Remote Support with RustDesk
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.