« Previous 1 2 3 4 Next »
Microsoft Exchange replacement
Top Dog in Sight
Getting Started
The software is available on GitHub [6] or as a packaged distribution from grommunio's customer repository service [7] or a community repository service [8]. Internally, grommunio uses the Open Build Service [9].
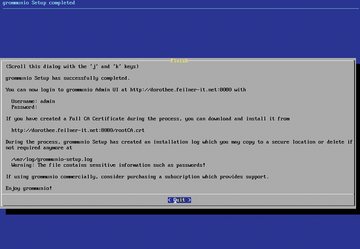
Initially, grommunio provides an ISO file that boots directly into the installation routine. After a reboot, the setup wizard waits for the initial configuration of the new grommunio instance. To begin, you import an existing SSL certificate or create a Let's Encrypt certificate with a supplied script.
Installation, configuration, and debugging take place on the grommunio console interface (Figure 4). The installation wizard asks whether it can delete the data on the first disk it finds. Afterward, grommunio shows you the admin login prompt and the decisions you made (Figure 5).
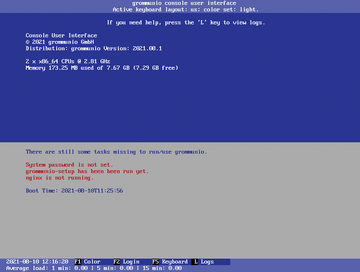 Figure 4: Before the installation, you need to log in by pressing F2 and possibly selecting the keyboard language with F5.
Figure 4: Before the installation, you need to log in by pressing F2 and possibly selecting the keyboard language with F5.
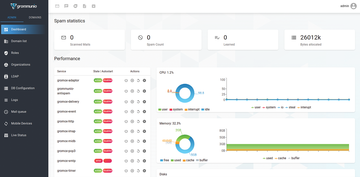
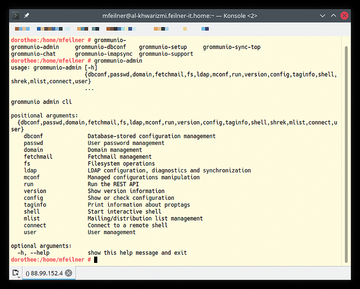
In the next step, you define further installation parameters like the correct mail domain(s). Regardless of the platform on which grommunio is installed, you can work at the grommunio command-line interface, in the admin graphical user interface (GUI), or from the web interface. Many options are available both in the browser (Figure 6) and in the shell (Figure 7), and users can enable individual modules for themselves in the web interface (Figure 8). For example, to add users to the mail domain, go to the Domain list section in the web interface.
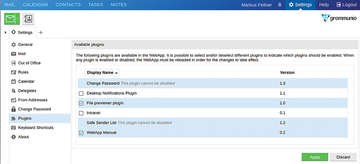 Figure 8: Whether desktop notifications or file previews, users can configure their modules in the web interface.
Figure 8: Whether desktop notifications or file previews, users can configure their modules in the web interface.
Because the ISO image is built on openSUSE, it uses the distribution's standard tools, including YaST for network configuration and Zypper for package management. The
zypper ref zypper up gromox-dbop -U
commands update the RPM packages and the database schema. A reboot is recommended afterward.
Performance
The closer the user to the software, the more important the performance for the acceptance of the chosen tool. Numerous failed open source groupware systems have already been forced to learn that a positive user experience with services such as email and calendars is massively dependent on responsiveness and speed. If it takes too long to receive mail, dissatisfaction spreads quickly. Components that cause a delay are discarded because of architectural decisions that imply massive hardware requirements for large setups. Well-coded software is always cheaper than new hardware.
Grommunio is aware of this phenomenon: The Vienna-based company refers to up to 50,000 active mailboxes on a high-end server, according to load tests and customer experience. Functional tests currently deliver promising results, which according to the developers is also due to the elegance of MAPI over HTTP: Microsoft has done a good job here, and grommunio also benefits. MAPI over HTTP is load-balanced and proxy-enabled and has proven to be very practical in terms of scalability – a task at which many open source groupware projects have already failed.
Closing the Gaps
Mail and groupware servers in the Microsoft cosmos are often a cyber battlefield. In the past, the largest malware attacks have always been routed through this infrastructure, and complete protection seems impossible. Although Outlook and Office 365 remain attack vectors with grommunio, two of the main entry points for hackers can be secured in a far better way: the groupware server itself and its operating system. No more Windows, no more waiting for patches and, on top of that, an open source community to help fix bugs and vulnerabilities – that sounds promising.
By default, grommunio runs on many Linux distributions on platforms ranging from the Z-series mainframe to the Raspberry Pi. Given a connection, an Active Directory or Lightweight Directory Access Protocol (LDAP) directories can act as an automatic source for usernames during authentication. Because the server integrates the Pluggable Authentication Modules (PAMs) built into Linux, tokens and all other known PAM solutions also work, provided the client supports challenge-response. The same applies to clients such as Outlook, Thunderbird, Apple Mail, Gmail, or Evolution: Whatever the operating systems allow, authentication works with the grommunio server in the same way as Microsoft Exchange.
« Previous 1 2 3 4 Next »
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Focus On Self-Hosting
• Self-Hosted PaaS with Coolify
• Build and Host Docker Images
• Self-Hosted Pritunl VPN Server with MFA
• Self-Hosted Chat Servers
• Self-Hosted Remote Support with RustDesk
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.