Lead Image © pitinan, 123RF.com
Post-Quantum Cryptography with TutaCrypt
Future Proof
Quantum computing represents a seismic shift in technology, promising breakthroughs in numerous fields. But for cryptography, quantum computers are a looming threat. Experts are well aware that traditional asymmetric encryption methods are at risk from quantum algorithms such as Shor's algorithm [1], which efficiently factorizes large numbers and could theoretically break RSA and elliptic curve cryptography (ECC). For symmetric encryption techniques such as AES, the quantum algorithm known as Grover's algorithm [2] halves the effective key length, thus requiring longer keys to maintain security. The looming end of conventional cryptography has caused mathematicians to search for a new kind of encryption that will resist quantum attacks. In order to succeed in the post-quantum world, a new generation of cryptographic algorithms will need to avoid the dependence on the discrete logarithm problem and the hardness of integer factorization of semiprimes characterizing classical approaches and rely, instead, on hashes, lattices, and other advanced techniques. Although quantum computers are still at the experimental stage, the IT world is already getting restless to know what will come next. Most cryptography customers want to encrypt their data permanently, not just until a bigger computer arrives. For that reason, some users are asking if it is possible to build quantum protection into existing crypto products now. With that need in mind, the email vendor Tuta [3] just rolled out a new version of their Tuta Mail product (Figure 1) that features quantum-resistant encryption, becoming one of the first commercial vendors to tackle this perplexing problem.
 Figure 1: Post-quantum encryption is a logical development for Tuta Mail, which has always been security focused.
Figure 1: Post-quantum encryption is a logical development for Tuta Mail, which has always been security focused.
The Algorithms
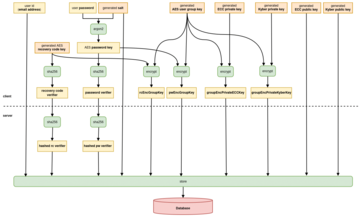
TutaCrypt [4] uses a combination of relatively new quantum-resistant algorithms and well-proven classical encryption to offer a hybrid protocol. The quantum-resistant component is Kyber [5], which was standardized as ML-KEM. Kyber, which is an outcome of NIST's Post-Quantum Cryptography competition, is a lattice-based key encapsulation mechanism (KEM). Its security relies on the Module Learning With Errors (M-LWE) problem, a difficult mathematical challenge even for quantum computers. In addition to its security properties, Kyber-1024 Key Pair offers excellent computational efficiency and comparatively small key and ciphertext sizes, making it well suited for resource-constrained environments such as mobile devices. TutaCrypt also uses two Diffie-Hellman key exchanges over Curve25519 (X25519) between static long-term identity keys and an ephemeral sender key (for randomized encryption and partial forward secrecy). X25519 is a well tested technique for Elliptic Curve Diffie-Hellman (ECDH) key exchange that provides strong security against classical adversaries. At the same time, the X25519 approach is highly efficient, requiring very short key sizes and computation times. In addition to safeguarding against impersonation attacks, X25519 ensures confidentiality against non-quantum adversaries even if weaknesses are discovered in Kyber in the future.
Once the shared secrets are established using Kyber and X25519, they are combined to derive a key for symmetric encryption with HKDF. TutaCrypt splits the key and encrypts email data with AES256 in CBC mode and then computes a tag over the resulting ciphertext with HMAC-SHA256, which yields authenticated encryption. AES is quantum-resistant with sufficiently long keys (256 bits) and provides efficient, authenticated encryption for bulk data. This hybrid approach is both tamperproof and highly efficient. By using both classical and post-quantum algorithms (Figure 2), TutaCrypt protects against unknown vulnerabilities in both realms. And the quantum-resistant components ensure that encrypted data intercepted today will remain secure against attacks from a future quantum computer.
The secret keys are wrapped with a password-derived key (Argon2id) and stored on Tuta's own servers in data centers in Germany. This approach means only the user can decrypt their private key to securely access their encrypted mailboxes, calendars, and contacts. TutaCrypt encrypts the entire email, including the body, subject line, and attachments, using this hybrid protocol. Using Elliptic Curve Diffie-Hellman (X25519), two shared secrets are exchanged between
- the sender's long-term identity key (IKA) and the recipient's identity key (IKB), and
- the sender's ephemeral key (EKA) and the recipient's identity key (IKB).
These secrets are referred to as DHI and DHE, respectively. A third shared secret, SSPQ, is exchanged using Kyber-1024's key encapsulation mechanism. The three shared secrets (DHI, DHE, SSPQ) are then combined via an HKDF-SHA-256 function to derive the encryption keys, and the keys are then used to encrypt and decrypt the message, ensuring confidentiality, integrity, and authenticity without requiring signatures.
TutaCrypt is already the default for newly created Tuta Mail accounts. Existing accounts still using traditional AES/RSA algorithms for asymmetric encryption will gradually transition to quantum-safe encryption once the key rotation mechanism is fully implemented. This phased rollout ensures minimal disruption while offering enhanced security for all Tuta users as quickly as possible. Tuta Mail is committed to ongoing improvements in cryptography. The company is currently working with partners at the University of Wuppertal to have TutaCrypt formally reviewed and verified. Tuta is also at work on new key verification mechanisms that will provide cryptographically guaranteed authentication. See the box entitled "TutaCrypt for Organizations" for more on how to implement Tuta's quantum-resistant cryptography in institutional settings.
TutaCrypt for Organizations
Tuta Mail's desktop, mobile, and web clients all come with the hybrid, quantum-safe encryption protocol. The desktop client is currently built for the following platforms:
- Windows as an nsis-installer
- macOs as a DMG for install and a ZIP for updates
- Linux as a self-contained AppImage executable
On Windows, you can set up the desktop client in enterprise mode by passing the following flags to the installer:
/S– install silently (no wizard)/allusers– install for all users on the system rather than just the current user (requires privilege escalation)/disableAutoUpdates– disable automatic updates (updates would need to be done manually by an admin)
You can uninstall silently by passing /S to the uninstaller (found in the installation directory under Program Files
). Administrators can bulk import employee email addresses using a CSV file with the following data:
*First Name,Last Name,Email Address,Role,Temporary Password*
After uploading the file via Tuta's admin console, users will need to receive credentials (email address and password, possibly also a second factor) and a link to download the Tuta Mail client. The Tuta admin settings allow the admin to manage users, change passwords, and revoke access in the case of a security incident.
Conclusion
Cryptography experts are already writing about all the ways quantum computers will break conventional encryption algorithms, and you can bet that spies and cybercriminals are well aware of the potential opportunities this will create. Given the rapid pace of development in the IT space, the "harvest now, decrypt later" (HNDL) attack is now a significant concern. Attackers could intercept encrypted communications today and store them until quantum computers are capable of decrypting them – and no one can predict when this is going to happen – next year or 10 years from now. TutaCrypt mitigates this risk by using quantum-resistant algorithms, ensuring data remains secure now as well as in the future.
Infos
- Shor's Algorithm: https://en.wikipedia.org/wiki/Shor%27s_algorithm
- Grover's Algorithm: https://en.wikipedia.org/wiki/Grover%27s_algorithm
- Tuta: https://tuta.com/
- TutaCrypt: https://tuta.com/documents/tuta-crypt-spec.pdf
- Kyber: https://pq-crystals.org/kyber/index.shtml
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.