« Previous 1 2 3 4 Next »
Securing and managing Microsoft IIS
The Right Tools
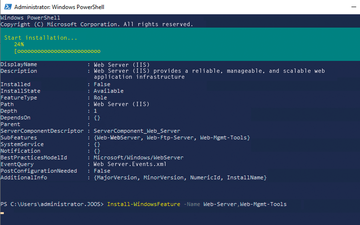
In this article, I look into the options Microsoft provides for effective management of Internet Information Services (IIS). You can easily manage web servers on Windows Server 2019 with multiple tools in parallel (e.g., the IISAdministration module in PowerShell). The command line on Windows servers also offers a way to manage the web server with the appcmd and iisreset tools, not only for servers with graphical user interfaces, but also for core servers and containers. In this article, I assume you have IIS configured on Windows Server 2019 (Figure 1), but most settings also apply to Windows Server 2012 R2 and 2016.
Managing the Web Server and Sites
Once IIS is up and running, it can be managed with the IIS Manager. The fastest way to launch this tool is to enter inetmgr.exe. If you do need to restart the IIS system service, you can use
net stop w3svc net start w3svc
or you can work with Stop-Service, Start-Service, or Restart-Service in PowerShell. In Windows Admin Center, you can use the Services
area. The system services themselves can be accessed by typing
Buy this article as PDF
(incl. VAT)
Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.