« Previous 1 2 3
Changes in Exchange Server 2013
New Clothes
During the installation of Exchange Server 2013 [1], you will notice that the new server offers far fewer options. Microsoft has dumped the Hub Transport and Unified Messaging server roles. The functions of these two roles are handled by the Mailbox server and the Client Access server in the new version.
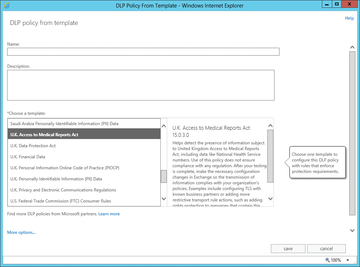
Email transport in Exchange Server 2013 is handled by three services: the Front End Transport Service (FET), the Hub Transport Service (HT), and the Mailbox Transport Service (MT), which now belong to the Mailbox server role. The transport services are also responsible for implementing the improved transport rules (Figure 1). The latter go by the name of Data Loss Prevention (DLP) and are designed to prevent sensitive data from leaving the corporate network. Also, Exchange Server 2013 integrates an antivirus scanner. The servers scan all incoming and outgoing email for viruses. Companies that rely on third-party antivirus scanners can disable this feature, of course.
Although Exchange Server 2013 can generally be installed in existing organizations with Exchange Server 2007/2010, you will need SP3 for Exchange Server 2010 and a hot fix for Exchange Server 2007. Older versions such as Exchange Server 2000/2003
...Buy ADMIN Magazine
Subscribe to our ADMIN Newsletters
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Most Popular
Support Our Work
ADMIN content is made possible with support from readers like you. Please consider contributing when you've found an article to be beneficial.